
Complex cyber ecosystems such as cloud computing offer great benefits but can leave your organization open to very costly liabilities.
 Trestle™ is a hierarchical security modeling and analysis application that gives you the ability to
Trestle™ is a hierarchical security modeling and analysis application that gives you the ability to
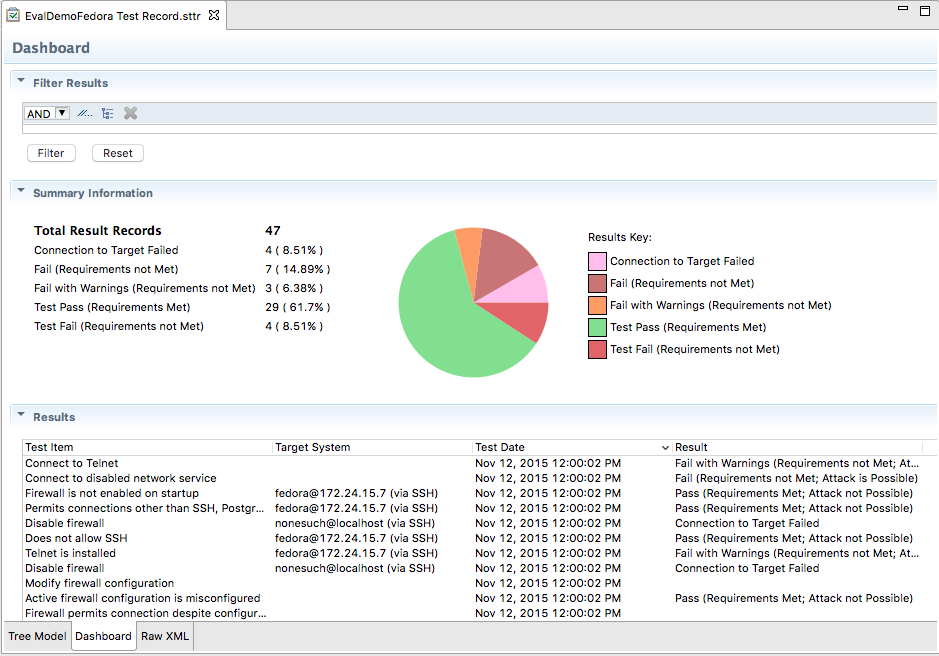
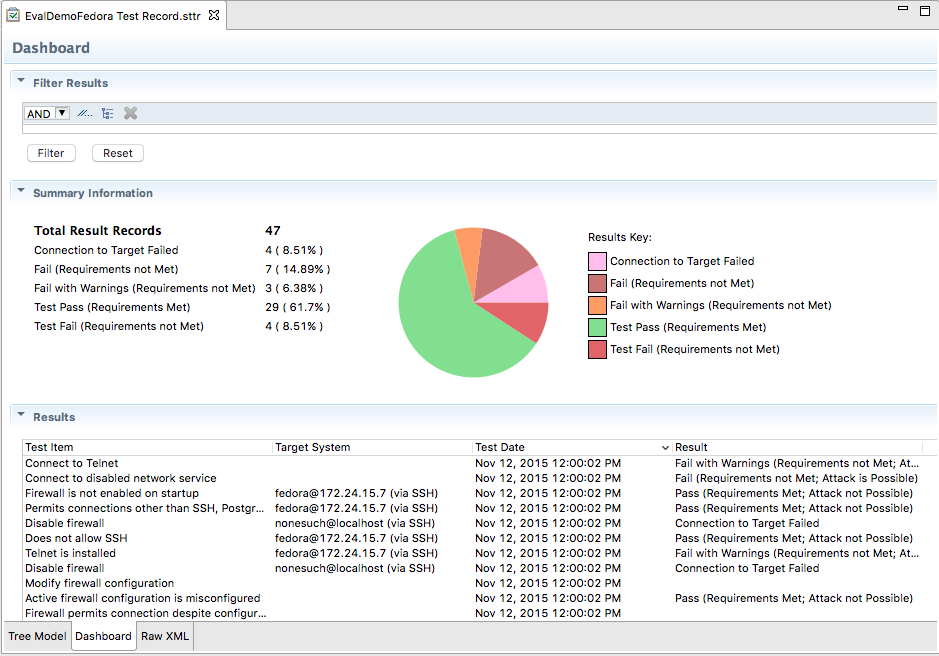
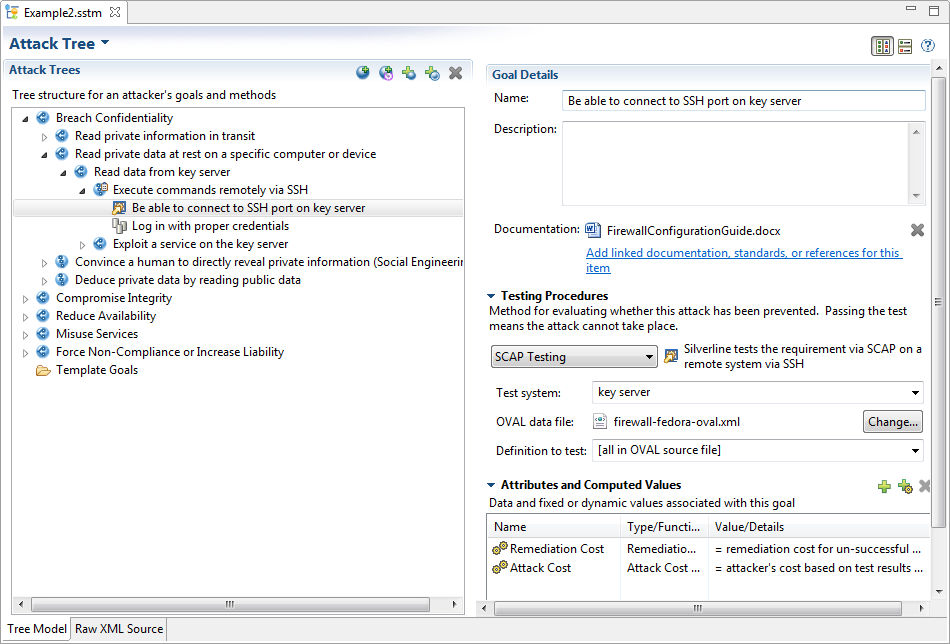
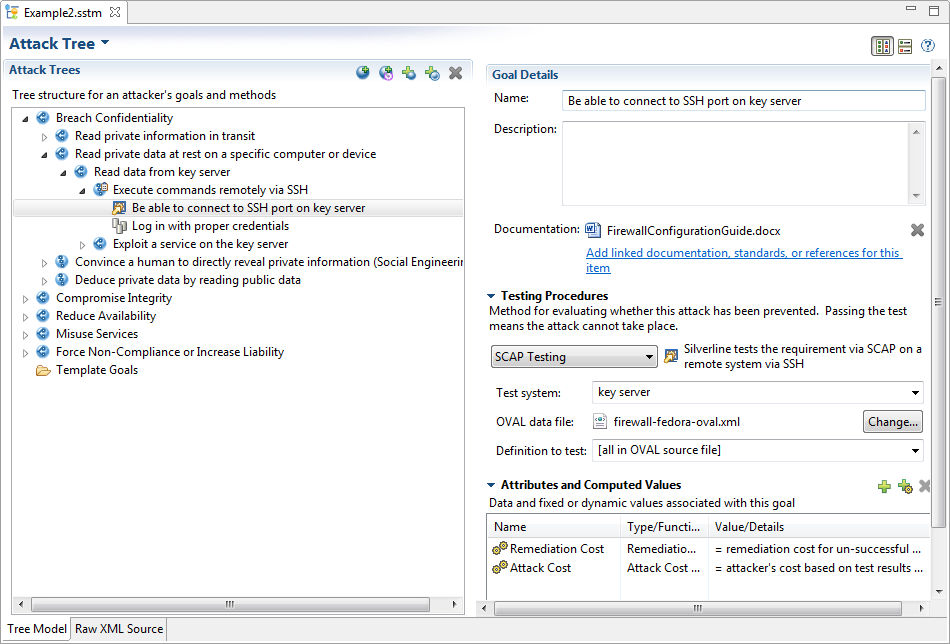
Performs on-line tests to determine whether modeled vulnerabilities are actually present, then presents results in context so you can see their impact.
Automates routine compliance testing to ensure new risks have not been introduced due to configuration changes by a cloud provider or due to newly-discovered software vulnerabilities.
Provides a structured, hierarchical framework for security models; no more reams of risk assessment text.
Uses a standards-based approach to extend host-based security analysis techniques to the cloud and large-scale systems.
Assists in assessing design tradeoffs.
Computes multiple tree-derived metrics, such as costs, impact, requirement analysis, or compliance.
Need to systematically document system security arguments?
Need to create attack trees at large scales?
Need to automate your security controls compliance monitoring?
Need to see at a glance what the most severe risks are?
Contact us at trestle@atcorp.com for more information.
Trestle’s graphical and command-line tools run on Microsoft® Windows 7 and newer, Apple® Mac OS X® 10.8 and newer, RedHat® Enterprise Linux® (or compatible) 6.x and newer, SUSE Linux Enterprise Server 11 SP2, and Ubuntu Linux 12.04 LTS and 14.04 LTS.