
CYRIN® is a next-generation “cyber range” platform for on-line interactive training and testing. CYRIN improves upon existing cyber range systems with three central innovations: (1) a fully interactive, independent on-line exercise environment for each student, (2) a graphical exercise builder, and (3) comprehensive monitoring of student progress against learning objectives within practical exercises. Combined, these innovations make effective on-line e-learning possible, saving money and time.
 Effective training for the next generation of cyber defenders and system analysts requires hands on exercises, where students learn by doing. Traditionally, this is done with a dedicated set of computer and network hardware on premises and in a dedicated classroom environment. Resource limitations typically prevent individual students or teams from having independent environments for their exercises, or from being able to roll back and “try again” if they encounter problems. Further, with current systems, instructors can only evaluate a student’s progress by monitoring them in-person and requiring that they meet an artificial goal, such as capturing a “flag” file. This traditional method is resource-intensive, inflexible, slow, and expensive and not very effective.
Effective training for the next generation of cyber defenders and system analysts requires hands on exercises, where students learn by doing. Traditionally, this is done with a dedicated set of computer and network hardware on premises and in a dedicated classroom environment. Resource limitations typically prevent individual students or teams from having independent environments for their exercises, or from being able to roll back and “try again” if they encounter problems. Further, with current systems, instructors can only evaluate a student’s progress by monitoring them in-person and requiring that they meet an artificial goal, such as capturing a “flag” file. This traditional method is resource-intensive, inflexible, slow, and expensive and not very effective.
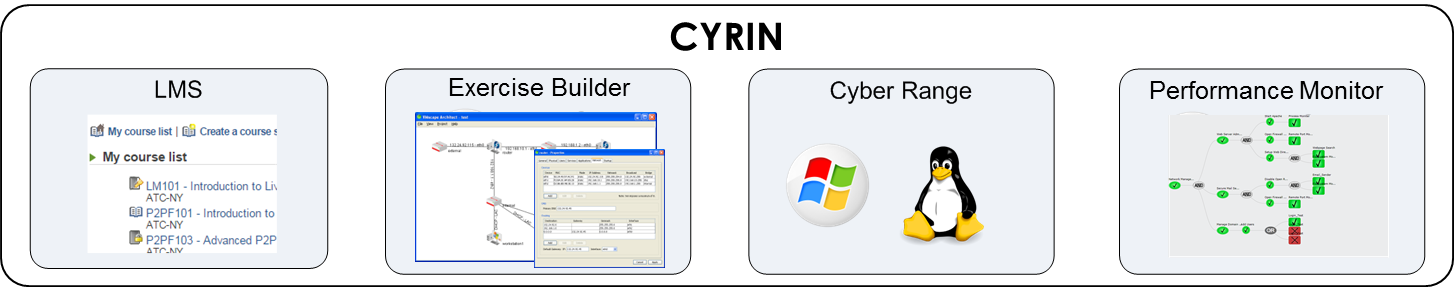
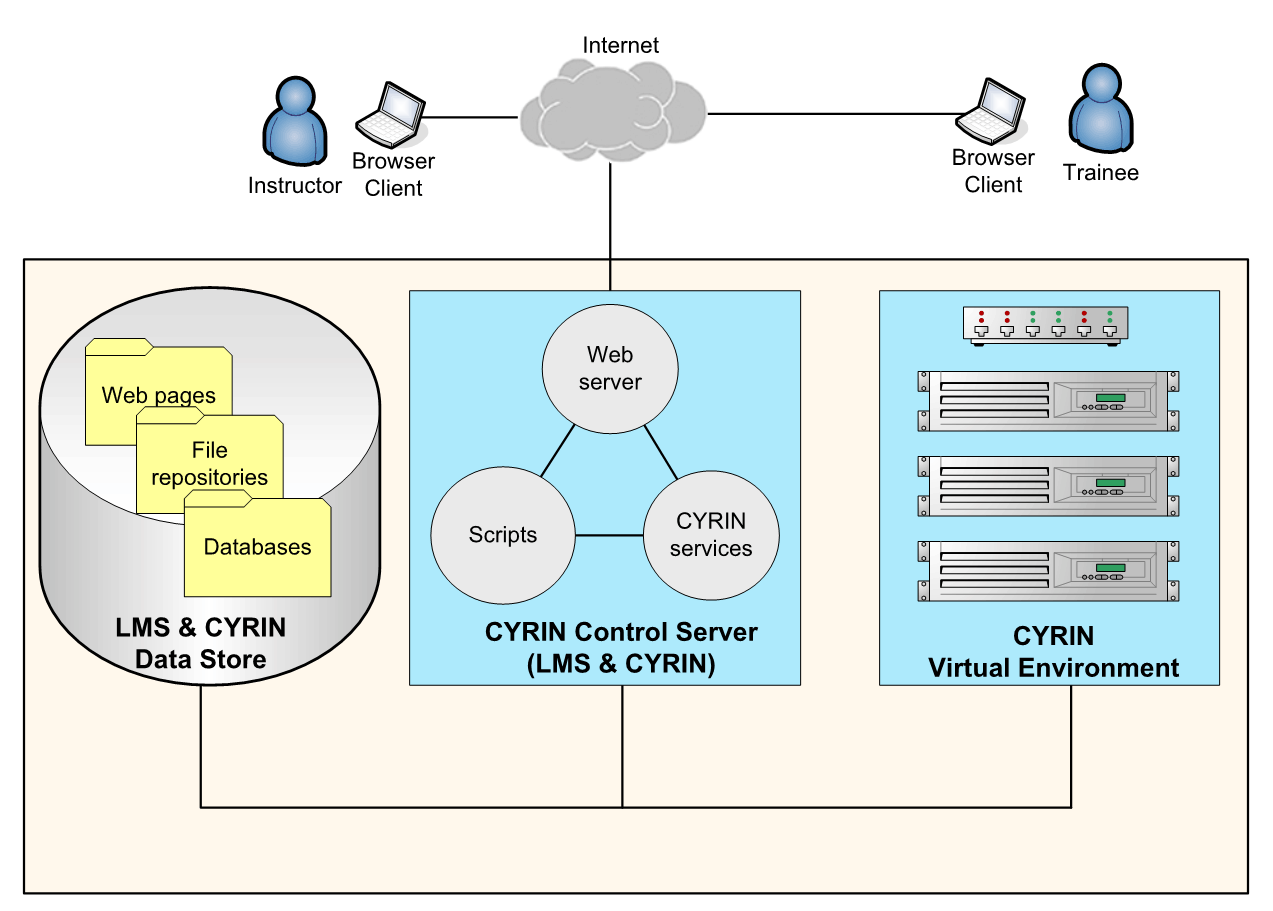
CYRIN is an advanced e-learning platform that integrates instruction, live exercises and performance monitoring and evaluation. The patented CYRIN platform consists of an on-demand virtual environment (cyber range), exercise creation tools, a learning management system, and an automated performance monitoring/evaluation system using remote agents.
Any of these technologies can easily be re-deployed to alternate environments. For example, CYRIN’s evaluation system and remote agents can easily be used with an existing cyber range, cloud service infrastructure, or physical hardware setup. CYRIN’s on-demand virtual environment can be integrated as part of an existing e-learning system.
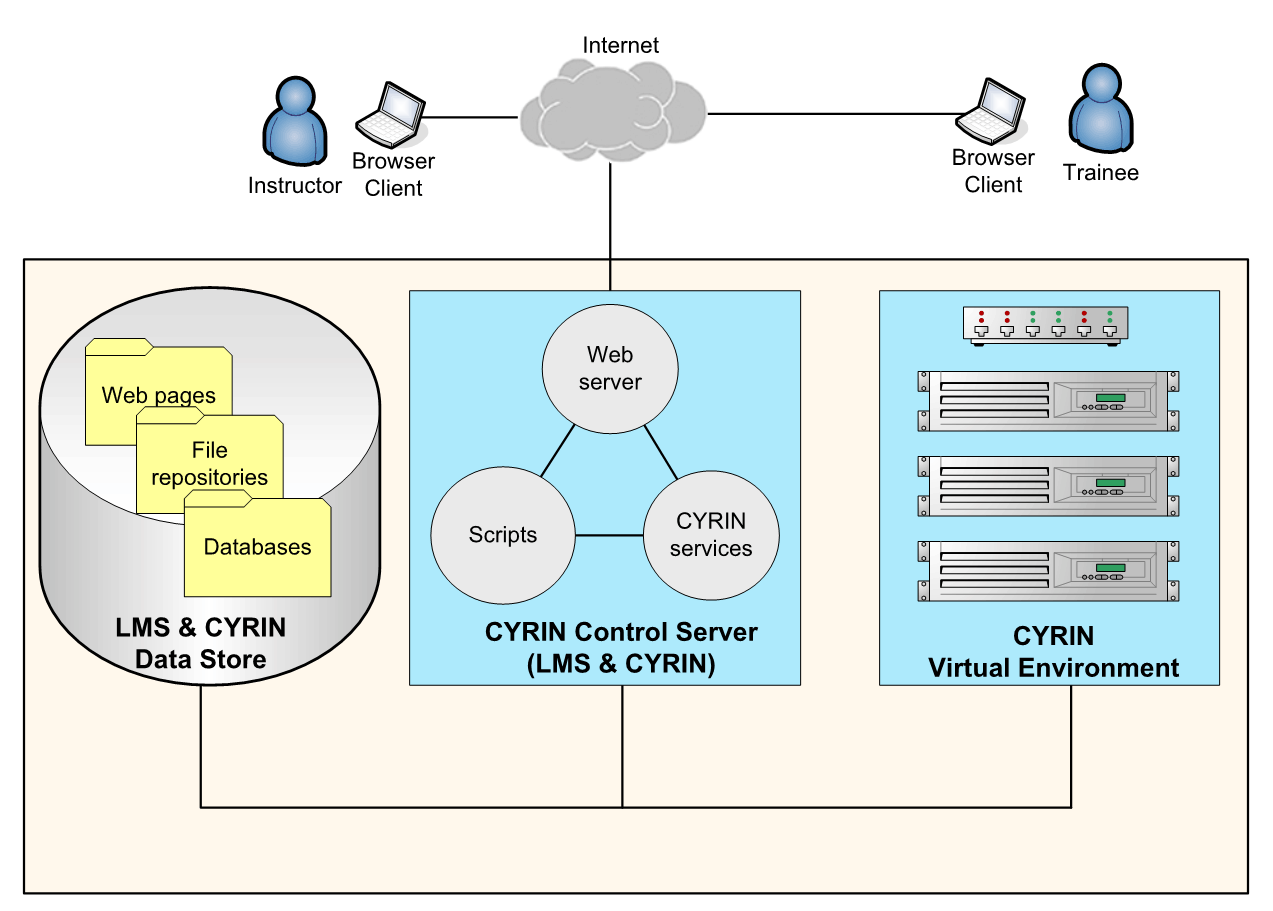 The CYRIN software suite can run as a small-scale, single-server on-premises deployment all the way through a cloud environment with virtually unlimited scale. Training scenarios can make use of any operating system that runs as a VMs guest on an Intel-based system: Windows 11, Linux, FreeBSD, VM-based appliances, and others. CYRIN’s monitoring agents come pre-compiled for Windows and Linux. For instructors and students, CYRIN is accessed via any modern web browser such as Google Chrome, Microsoft Edge, Apple Safari, or Mozilla Firefox.
The CYRIN software suite can run as a small-scale, single-server on-premises deployment all the way through a cloud environment with virtually unlimited scale. Training scenarios can make use of any operating system that runs as a VMs guest on an Intel-based system: Windows 11, Linux, FreeBSD, VM-based appliances, and others. CYRIN’s monitoring agents come pre-compiled for Windows and Linux. For instructors and students, CYRIN is accessed via any modern web browser such as Google Chrome, Microsoft Edge, Apple Safari, or Mozilla Firefox.
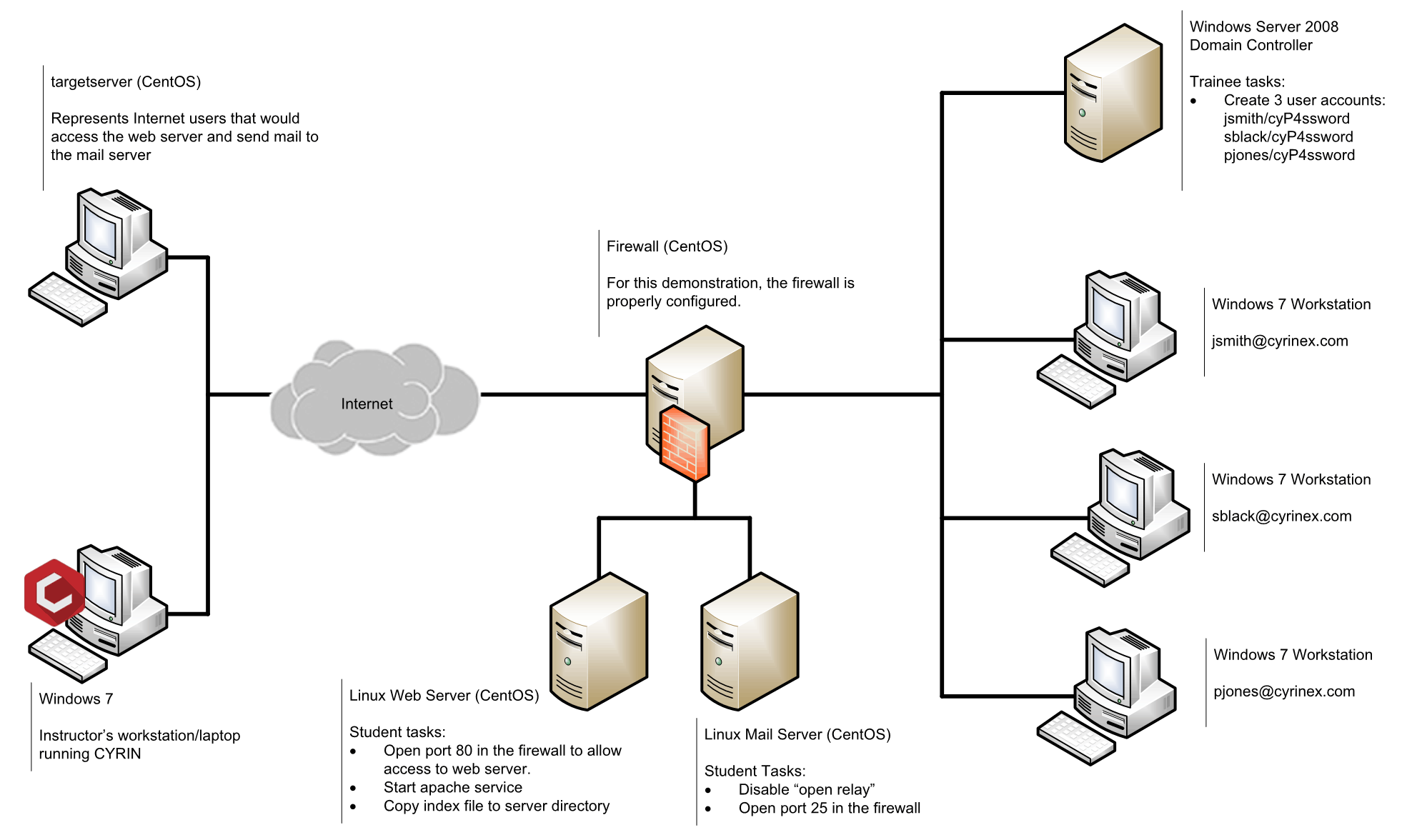
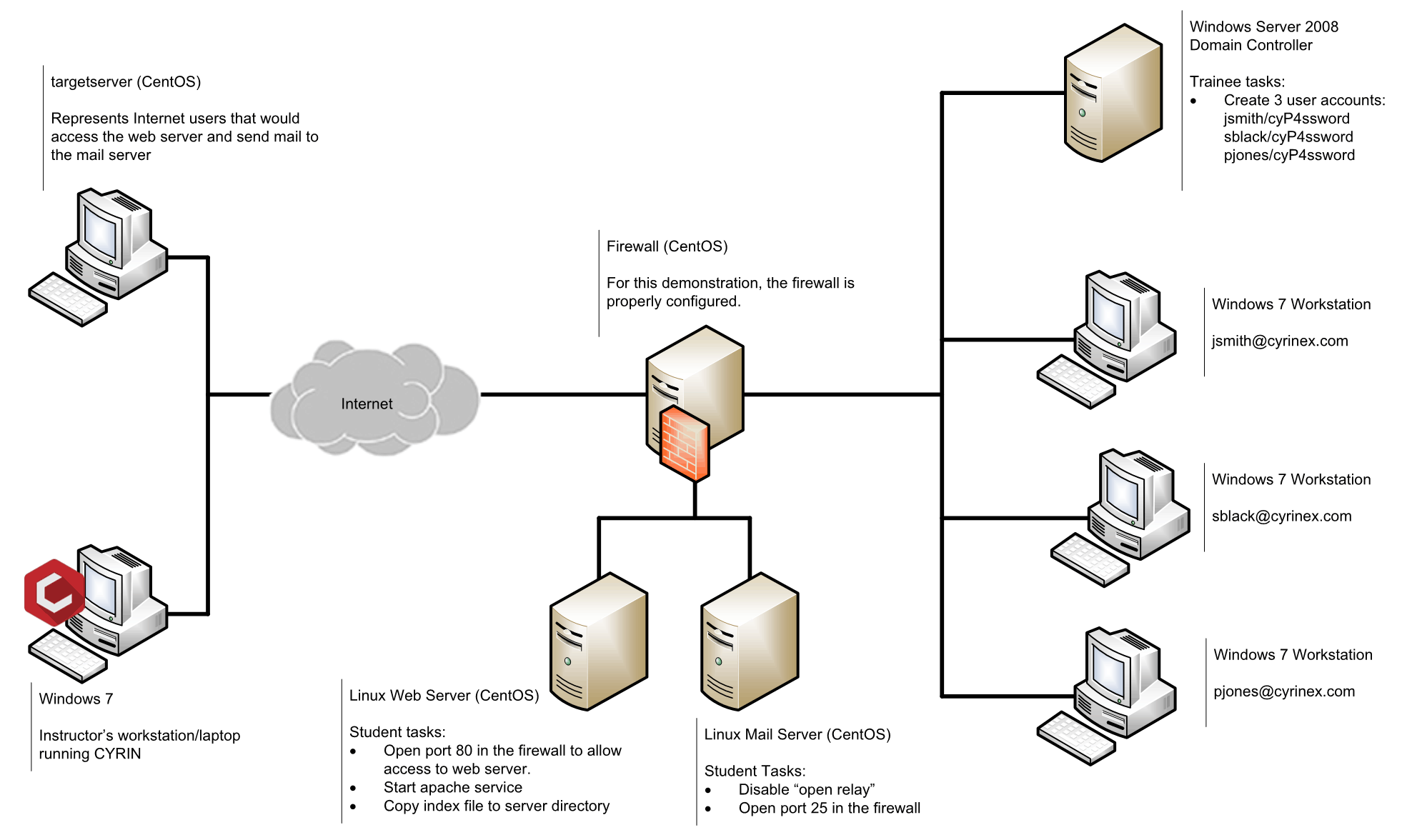
The CYRIN platform incorporates an extremely efficient exercise development module allowing training staff to quickly develop and deploy student exercises. Sample CYRIN exercises include:
Student must finish configuring and starting a new web server on Linux systems, then must respond to a distributed denial of service attack and restore the server’s availability.
Students use a site-specific graphical forensic tool on Windows to extract information on P2P file sharing usage. CYRIN’s virtual environment provides access to very large sample data sets and eliminates the need for students to install and configure site-specific software on their own systems.
Red team students attempt to upload malware to an FTP server, either anonymously or by brute-forcing a password. Blue team students prevent the attack in multiple ways. Each Red Team participant has his/her own dedicated virtual machine and can initiate specific attacks simultaneously or with other Red Team members. Blue Team defenders also have their own virtual machines and can react individually or as a group to protect their part of the network.
A student executes a host or network-based attack in order to act as a man-in-the-middle in front of a critical service. For example, the student can execute a network-level attack within CYRIN to redirect all communication between the victim and a bank’s web site, viewing and/or altering account information. A student tasked with network defense can configure the systems to avoid such attacks or mitigate the effects of an attack after it has taken place.
CYRIN Sales Team
Email: sales@cyrintraining.com
Phone: +1-800-850-2170
...or simply visit cyrin.atcorp.com